It's been compared to Ocean's Eleven - a cyber attack on Australia's top university, methodically planned and then adapted on the fly by an "A team" of hackers who cracked into the personal records of 200,000 students and staff and walked away leaving virtually no trace.
Subscribe now for unlimited access.
$0/
(min cost $0)
or signup to continue reading
The operation was so slick investigators claim they still don't know if the breach was the work of a foreign state, even as its "shocking" sophistication throws suspicion on China.
But the hack didn't go entirely to plan. Now, after months of forensic analysis, the Australian National University has revealed it's likely the hackers "didn't get what they wanted" from its records after all. They were foiled in the act - and it was entirely by accident.

On Wednesday, the university released a post-mortem of the hack and how staff responded - the first public report of its kind into an Australian cyber attack. It describes a highly professional operation, likely of up to 15 people "working round the clock" to harvest data and build custom malware within the network itself.
Hackers evolved, covered their tracks and returned for fresh attacks when a scheduled fire wall unexpected booted them out, in a campaign the university says was remarkably more sophisticated and "distinct" from an earlier breach involving national defence research in 2018. If the university hadn't been cleaning up after that hack, where nothing was stolen but suspicion also fell heavily on China, it's unlikely staff would have discovered this second breach when they did.
"Frustratingly" the ANU says it doesn't have enough evidence to point the finger at anyone this time around, not even organised crime - security teams now scouring the dark web for the stolen data have turned up nothing so far.
Director of defence, strategy and national security at the Australian Strategic Policy Institute Michael Shoebridge has read the report closely ("It's bit like CSI Miami") and thinks China remains the most likely suspect - both for its well-known cyber capability and its interest in harvesting human intelligence on Australian government officials and researchers known to orbit the ANU.
So how did the hackers get in and what clues did they leave behind?
According to the report, which was developed in collaboration with Australia's security agencies, the intrusion was first discovered in April, during a routine security sweep. A small army of cyber experts descended on the campus and the hunt began in earnest, with staff realising on May 17 someone hadn't just been in the house, they'd been robbed. More than two weeks later, vice-chancellor Brian Schmidt went public with the news: the university had been hacked for the second time in less than a year. Nineteen years' worth of HR data had been compromised.
The final report now revises down that figure considerably - while hackers got into that database, analysts believe they stolen only a fraction of that, or roughly the same amount you can store on a CD. But to date investigators are still not sure exactly how much data was taken - or why.
Professor Schmidt handed down the report on Wednesday with an apology to students and staff and a call to break the silence surrounding attacks of this kind.
He said he hoped its detail would encourage disclosure about hacks more broadly, rather than providing an "instruction manual". In the interest of transparency, only a small number of very specific details were omitted to prevent copycats.
The hack was so sophisticated it "has shocked even the most experienced Australian security experts", Professor Schmidt said, though he acknowledged the university "could have done more".
"This wasn't a smash and grab, it was a diamond heist," he said. "It's likely they spent months planning this. They were organised and everyone knew their role."
How did hackers get in?
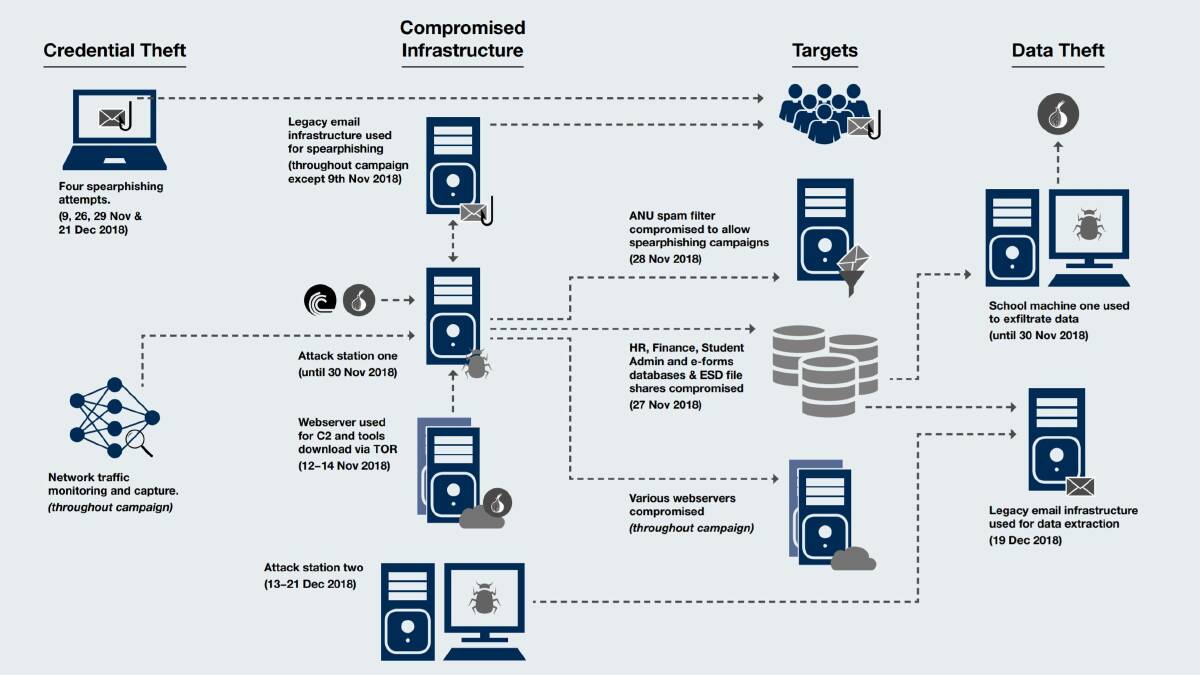
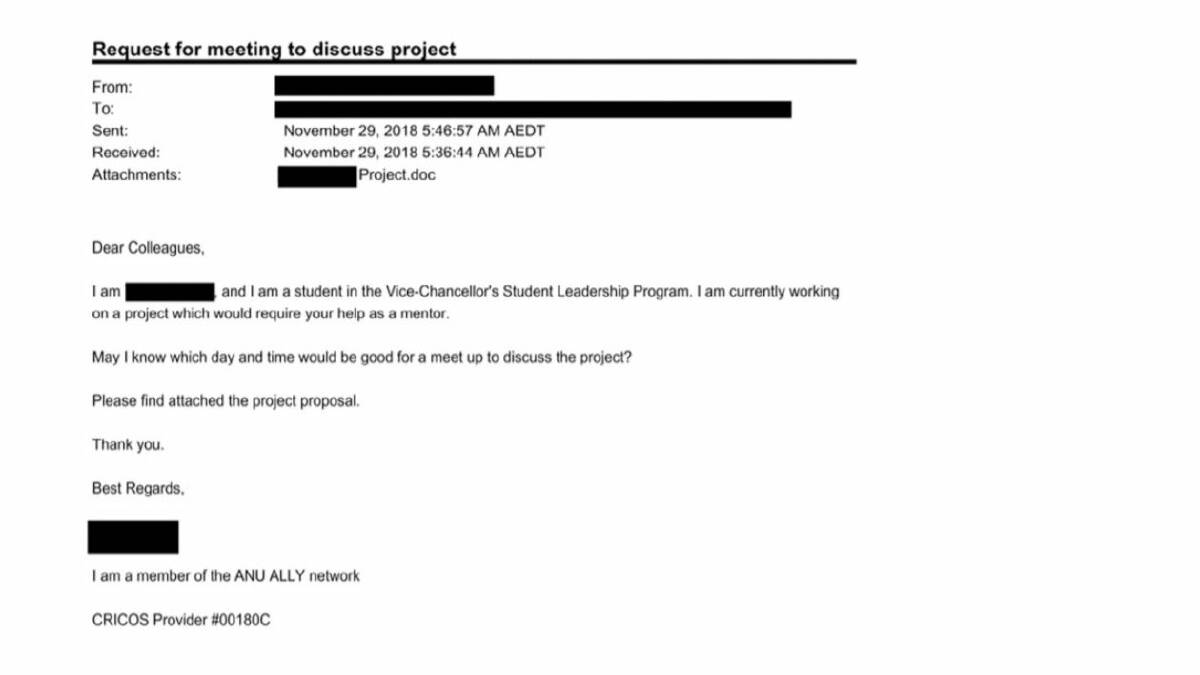
It began, as many attacks do, with a seemingly innocuous email sent to a senior staff member in November 2018. The staffer wasn't on campus at the time so it was read by a colleague. And they didn't open the attachment. But this was something a little more sophisticated than the usual nefarious traffic the university deflects from its inboxes (ANU blocks 5000 intrusions attempts a day). Just previewing this email's attachment was enough to deliver the malware and steal senior login credentials. And the hackers had their first door in.
"The fact they got in without anyone actually clicking on an email, that wasn't widely known around the traps," Professor Schmidt says. "We were sort of ground zero for that."
From there, investigators think hackers must have gotten got lucky - an inside job has now been ruled out.
The thieves managed to find an old legacy server due to be decommissioned within the year and it was there that they built their base of operations, installing "shadow infrastructure" to cloak their movements on the network as they hunted for a way into its more secure databases.
What was the target?
Investigators say they are confident they know what the hackers were after - the HR files - because they made a beeline for that part of the network to the exclusion of other areas like research, much of which they had also gained access to.
While the hackers ran extensive software to clean up their trail, university analysts believe they would have found traces elsewhere, as they did with the HR database, if they had been busy in more than one place.
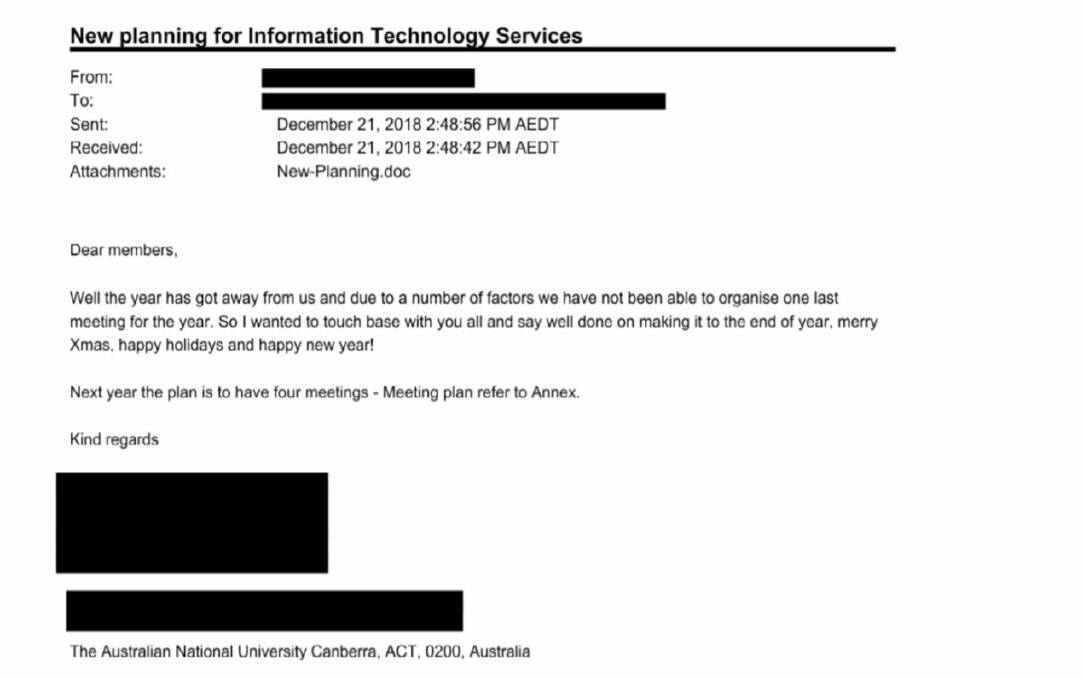
Instead, even when inside the network, they used password cracking software and kept running email "spear-phishing" campaigns like the one that first worked in November - trying to sniff out the right credentials to access the closed HR system, and eventually taking a final, desperate run at the IT department itself.
What did they actually steal?
Once they broke into the HR database through a previously unknown vulnerability, hackers used their own custom-made software to scrape its data so detail of exactly what was taken wouldn't appear on ANU logs. But university investigators are confident the amount taken was much smaller than they originally thought - megabytes out of the many terabytes of information stored in the data-set.
Spanning a period of 19 years, the affected HR records include payslips, bank account details, tax file and passport numbers, emergency contacts, and some academic records, on an estimated 200,000 current and former staff and students. Sensitive personal information such as medical and counselling records, academic misconduct and financial hardship is not stored in the same part of the network.
Whether the data was taken based off a targeted search of the records, a random sample or some other extraction method is still unclear.
How was the hack discovered?
But the intruders didn't stop there.
After extracting the HR files via another compromised computer, more phishing emails were sent out to harvest further credentials.
Whatever hackers planned to do next, they were interrupted. A new scheduled firewall went up, booting them out of their base of operations in the middle of one of their clean-up cycles.
They spent a frantic fortnight in the lead up to Christmas trying to break back in. Eventually, they found another foothold in a legacy computer not behind a firewall.
But what about those email traps sent to IT staff?
As hackers continued their operation, one or two red-faced IT staffers did click on their malicious emails, handing over more credentials.
But others in the department recognised the emails for what they were and shut down the new attack station. Unfortunately, at the time, they didn't see them as part of a much bigger attack.
Unknown to the university, hackers were now waging another a two-month-long battle to get back inside its systems.
Were they after more than just the data?
For the ANU's chief information security officer Suthagar Seevartnam, all this suggests the information they stole wasn't the endgame after all.
Part of the data harvested was made up of field names, often displayed in confusing jargon unique to the university. It would have been difficult for hackers to search and, indeed, decipher. And the ANU says what was taken doesn't appear to have been misused.
"Our current sense is the actor didn't get what they wanted because they were stopped twice during their campaign," Seevartnam says. "And what they did get was not immediately usable or they didn't understand the data's business context."
Once disrupted by ANU security upgrades, the hackers didn't give up, trying new tactics almost up until the point of discovery, including attempts to disable the university's email spam filter. They also returned to harvest another handful of HR files missed during the first extraction.
Even after discovering the breach, the ANU says it was still under attack, working to shore up its defences and secure the network.
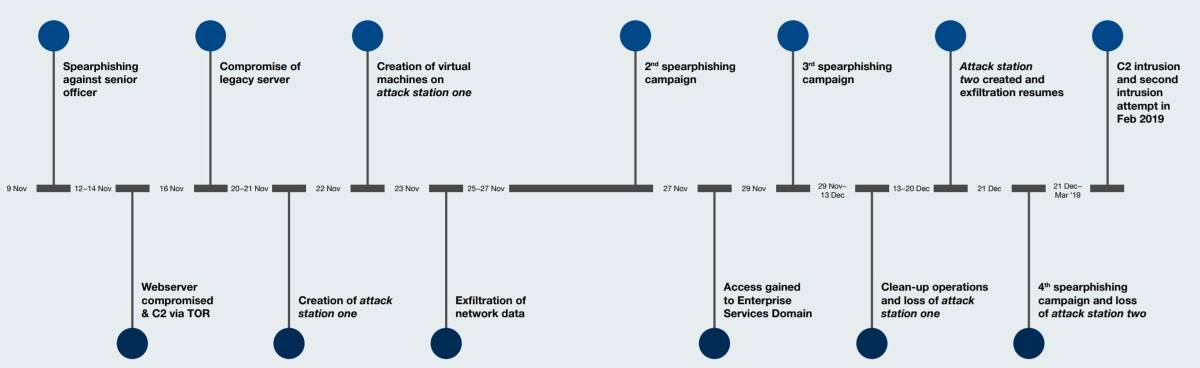
Within an hour of going public with the news, the university came under fire again, this time in the form of a botnet campaign. And the following night, there was another attempt on the spam filter - leading investigators to suspect the same hackers still hadn't given up.
The university now believes its systems are secure.
Who was behind it?
Whoever they were, they were well-resourced and highly skilled. As Professor Schmidt puts it: "This was a state-of-the-art hack, carried out by an actor at the very top of their game, at the very cutting edge."
Sophisticated is often code for "state sponsored" but at this stage the ANU insists it can't rule anyone out.
While it notes the type of data targeted - HR and financial records - would be of high value to criminals dealing in identity theft online, the information stolen hasn't been detected online
And both the university and police say the small number of suspected identity fraud cases involving ANU staff or students since the breach have all been deemed unrelated.
So did hackers keep going because what they extracted wasn't valuable enough to sell - or were they after something else?
Shoebridge thinks it unlikely the type of data taken would have been of much interest to criminals in the first place.
"They have better sources for that kind of stuff," he says. "But universities are great datasets for foreign espionage outfits. This would fit nicely into information China has already gotten elsewhere.
"ANU conducts a whole lot of interesting research, it's student and teaching population over time flow on to become government officials.You need information on people to pressure them into doing what you want.
"The level of sophistication and aggression here calls to mind a state actor. It's pretty impressive ANU found them. I think they would have been happy to stay in the network, undetected."
What do security agencies think?
Attribution is a notoriously difficult on the modern cyber battlefield. As countries throughout the world devote more resources to online spying and sabotage, diplomacy is struggling to keep the peace.
The Australian Cyber Security Centre, which is run by the nation's top spy agencies, did not respond to requests for comment before deadline but has been working closely with the ANU on the investigation.
Last year, the centre's head Alastair MacGibbon said he was aware of foreign countries that "actively try to steal IP from tertiary institutions and research centres" and last year the Australian government took the rare step of publicly rebuking China for stealing commercial secrets from local businesses. But this hack has not been attributed to the communist government so far.
Shoebridge thinks attribution is important.
"This should serve a lesson for all institutions, especially universities," he says. "But it shouldn't be on them to take on foreign governments. Australia needs to attribute attacks like these. If you catch a burglar in your house, pretending it didn't happen just encourages them to come back the next night."
What is ANU doing now?
Having identified technical weak-points in ANU systems as well as "people and process issues", the university will now look to rebuild its network entirely over the next four years and roll out extra training to staff. The university did not answer questions on funding for the new initiative or IT resources during the hack, but at the time it was discovered staff were in the middle of a significant security upgrade following the previous 2018 attack.
"Unfortunately, there was not sufficient time to universally implement all measures across the ANU network between the two attacks in 2018," the report says.
"The sophistication and speed of the second attack underscore the threat environment in which we now operate."
ANU handed down the report as Australia's top spy agency launched an investigation into another attack on regional Victorian hospitals this week.
Seevaratnam says commentary around hacks should focus less on what organisations did wrong - which he calls "victim-blaming" - and more on the lessons that can be learnt to protect the community.
"We need to encourage and support other victims coming forward and sharing their stories."

